News
European Promotion of the SHARE Foundation’s Book on Biometric Surveillance
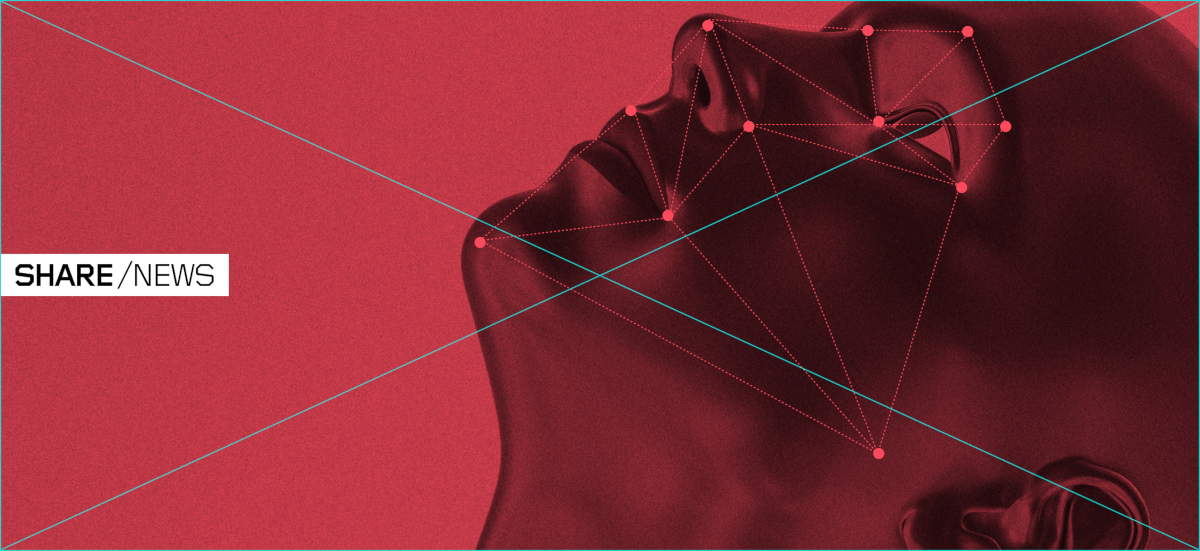
One of the most comprehensive studies on the use of biometric systems worldwide, the SHARE Foundation’s book “Beyond the Face: Biometrics and Society” was presented on Monday, December 4, in Berlin and on Wednesday, December 6, in Brussels.
The promotion brought together the community for the protection of digital rights and freedoms at the Tactical Tech premises in Berlin, where the authors and attendees discussed the legal and social consequences of mass biometric surveillance.

In Brussels, a discussion was organised in the European Parliament on the study’s key findings, with opening remarks given by Members of the European Parliament Viola von Cramon and Sergey Lagodinsky. As an urgent danger, the MEPs pointed to a potential precedent in Serbia with the application of biometric surveillance technology towards the creation of a dystopian surveillance society. Patrick Breyer, also a member of the European Parliament, took part in the discussion.
Coincidentally, the book promotion in Brussels took place during the final stages of the trilogue on the new European regulation on artificial intelligence (AI Act). In fact, after the event MEP Lagodinsky moved on to the negotiations on banning of unacceptably risky systems, carrying his own copy of the book. The impact of the AI Act will have far-reaching consequences for the regulation and use of biometric surveillance systems around the world. Thus the importance of such detailed analysis of the biometric surveillance application in different countries, contesting problematic provisions of the future European law that could legitimise these practices.

The study on the social consequences of mass biometric surveillance provides a detailed description of technologies from various manufacturers used by public and private actors for surveillance. It includes a comparative analysis of regulations governing this field in the US, the EU, and a range of countries in Africa, Asia, and Latin America. Additionally, it explores some practical cases of biometric surveillance application, from Myanmar and the United Kingdom to New York and Belgrade, for border control, public space monitoring in major cities, or suppression of opposition activities.
Spanning over 300 pages, divided into three main segments—Technology, Law, Practice—the book acquaints readers with the current global experience of the conflict between fundamental human rights and the profit-driven biometric surveillance industry. Despite abundant evidence, authorities worldwide still believe that these systems contribute to the security of society.
The book is freely available, currently only in English. The editors of the publication are Ella Jakubowska (EDRi) and Andrej Petrovski & Danilo Krivokapić (SHARE). The authors of the texts are Bojan Perkov (Technology), Jelena Adamović and Duje Kozomara (Law), Mila Bajić and Duje Prkut (Practice).